5月12日晚,勒索病毒“WannaCry”感染事件在全球爆发,病毒已经扩散至全球上百个国家和地区,并造成超过7.5万起电脑病毒攻击事件 。该勒索软件对于企业局域网或内网的主机系统破坏性尤其严重,据360数据显示,仅上周五、周六两天,国内出现了29000多个感染了该勒索病毒的IP,本次病毒事件波及教育科研单位、商业中心、医疗单位等等,情况十分严峻。据阿里云首席安全研究员吴翰清分析,“这次蠕虫式传播的病毒是 2.0 版本,而在之前还有1.0 版本。”那之后是否还会出现3.0版本、4.0版本……勒索病毒只能预防,中毒文件不可恢复
WannaCry勒索病毒和CIH病毒、熊猫烧香、冰河木马、Worm_Vobfus蠕虫等病毒不是一个级别的,WannaCry勒索病毒只能防,破解只存在理论可能,而目前全世界仍然无解,企业一旦中毒,核心数据资产文件不可恢复,对于中毒企业而言将是一场毁灭性的灾难,还没中毒的企业必须第一时间预防WannaCry勒索病毒。
通过百度指数查询“病毒查杀”、“备份软件”、“数据备份”代表用户对文件备份和病毒查杀需求的部分关键词发现,5月13日之后,三类词汇在百度上的检索量呈上升趋势,且在5月15日(周一以及第二波病毒来袭)时呈明显增长,从病毒的传播情况判断,用户对文件备份和病毒查杀的关注度和需求会持续走高,侧面反映出病毒出现前用户不重视文件备份甚至不知道如何进行文件备份,以至于病毒出现后由于担心重要数字资产的丢失而恐慌。
企业文件安全遭威胁,WannaCry勒索病毒并非首例
WannaCry勒索病毒的爆发,是在为中国企业文件安全保护又一次敲响了一个警钟。在企业为预防病毒手忙脚乱的同时,企业是否还记得在过去几年还有很多其他各类的安全事件严重威胁着企业文件的安全?因为文件保护不到位而丢失或者无法修复的真实案例信手拈来。
- 病毒感染导致文件无法修复
2015年5月,比特币病毒CTB-Locker横行,主要通过邮件附件传播,因敲诈金额较高,该类木马投放精准,瞄准“有钱人”,通过大企业邮箱、高级餐厅官网等方式传播,中木马后,虽然可以使用杀毒软件杀掉该木马,但加密文件没有任何办法还原。短短几日已造成国内上千台电脑中招,其中不乏国内众多知名企业,保守估计造成经济损失可能会达到上千万元。病毒感染导致企业文件无法修复不仅为企业造成巨额的经济损失,更是为构建企业核心数字资产大脑增加阻力,迫使企业发展放缓。
- 员工电脑硬盘损坏公司核心资料永久丢失
今年4月初,重庆的王先生电脑硬盘损坏,他的电脑要储存许多宝贵的工作资料和数据,为了安全,就选择了某品牌的固态硬盘,因为它号称安全性非常高,没想到才2年多时间这个硬盘反复出问题,已经坏三次了,这次里面数据全部丢失,包括表单等工作数据以及跟一所大学项目合作是为其撰写的调查报告,整个数据价值3万~5万元。”硬盘损坏丢失的不仅是资料,还有企业在合作方中的可信赖度,后续合作也必然受到影响。
- 员工离职致大量机密资料泄露
近日,老干妈公司离职人员贾某涉嫌侵犯商业秘密案,已被刑事拘留的事件炒的沸沸扬扬。2003年至2015年4月,贾某历任老干妈公司质量部技术员、工程师等职,掌握老干妈公司专有技术、生产工艺等核心机密信息。2015年11月,贾某以假名做掩护在本地另一家食品加工企业任职,从事质量技术管理相关的工作。在本起涉嫌商业秘密泄露的案件中,办案侦查员搜查扣押了贾某随身携带的移动硬盘及内含的电子证据资料,并在其台式电脑中发现大量涉及老干妈公司商业秘密的内部资料。离职后随意将机密资料带走,贾某商业泄密案坐实,对老干妈公司而言,仿冒品带来的除了是经济损失,名誉损失才更至关重要。
无论是病毒感染,员工电脑硬盘损坏还是老干妈离职员工通过移动硬盘轻易带走公司核心数据资产等,都会让人反思,国内对文件没有统一管控的企业并不少,潜伏的文件丢失、商业机密泄露等危机会不会集中爆发?
或许,WannaCry勒索病毒的这次爆发就是一堂企业文件安全保护的启蒙课,让这个企业里最大的安全隐患再一次的回归到了我们的视线。
80%核心资产有风险,再丢一次很可怕
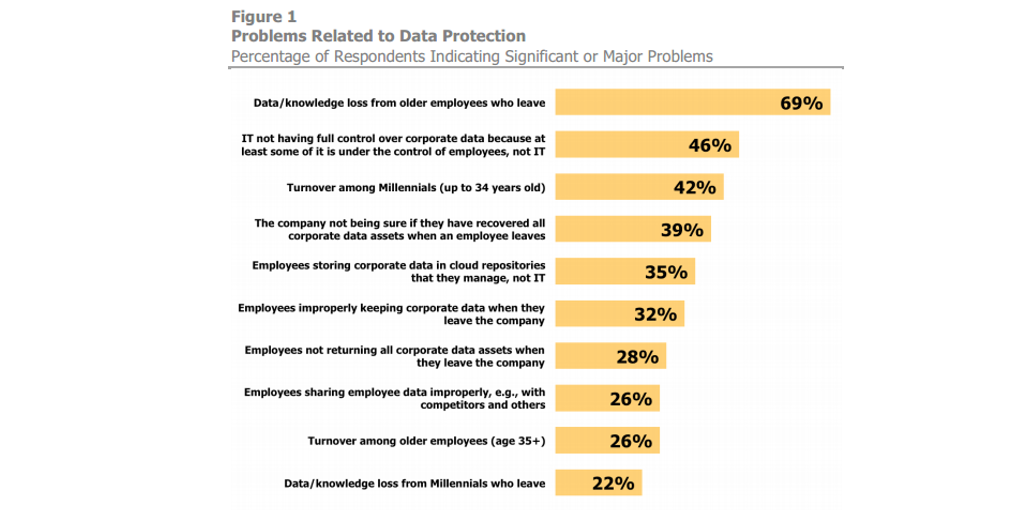
在过去的几年,我们谈到企业大数据,更多是讨论企业的结构化数据,也就是存在于数据库中的企业的生产数据、交易数据、销售数据等等,这些数据存储相对集中,比较容易通过不同的数据应用提取对业务有帮助的分析价值。目前企业普遍还没有对另一类规模更大、价值更高的数据产生足够的关注,这些数据是以各种文档、图片、视频、音频文件为代表的非结构化数据。这类数据目前处于极度分散的状态,而他们往往承载的是企业商业价值最核心的知识/商业信息,这些数据的丢失、泄露或者无法访问共享都会给企业的信息安全、知识传承和业务效率带来极大的影响。美国奥斯特曼研究公司(Osterman Research)在 2016 年的一份白皮书报告中,对北美 187 位来自IT/HR领域的人员深入调查,分析员工离职对企业信息安全的影响,详情请见下表:
随着互联网云计算的发展,非结构化数据的数量日趋增大。据统计,当前非结构化数据的内容占据了数据海洋的80%,并将在2020年之前以44倍的速度迅猛增长。
数字时代即将到来,非结构化数据是企业绝大部门的工作产出,企业的知识大脑,企业商业价值的导体,它的安全性却并没有被企事业单位高度重视,甚至没有对非结构化数据进行统一的备份和存储,更不用说管理和能产生更大价值的协作。WannaCry勒索病毒的这次爆发只是其中一种导致企业文件安全风险的因素,企业需要从现在起系统化的对文件进行安全保护,因为这些最重要的数据可能再丢一次就永远找不回来了。
保护企业信息安全,专家建议这么做
亿方云就“企业信息安全管理”问题联系到DNV GL大中国区BCM(业务连续性管理)产品经理宋琳女士(注:DNV GL是中国信息安全及云安全认证领域的领导者,为国内包括腾讯、网易等企业提供服务)。宋琳女士认为,“如今多数企业安全事件的发生和安全隐患的存在,30%可能是技术的原因,但更大可能说是管理不善造成的,理解并重视信息安全管理对于企业运营的作用,将技术手段和管理措施落地,对于实现企业信息安全目标来说尤其重要”。
企业对各类信息资产的保护以及企业IT平台的高可用性,是信息安全的重要目标,在企业信息安全管理建设中,宋琳女士提出很多实操性建议,总结为下面两方面:
识别重要的信息资产
信息资产的存在形式有多种,纸张、各种介质、服务器、PC机、照片甚至手机邮件等。信息资产概括总结为五点:
- 软件;
- 硬件:包括服务器及相关的基础设施如网络等;
- 存在于各个应用系统内的结构化数据信息;
- 员工日常使用的文档、图片等非结构化数据信息;
- 企业内外所有可能接触到敏感信息的人员。
信息资产风险处理
信息资产处理策略可按照降低风险、规避风险、转移风险和接受风险四步骤。
- 降低风险——针对风险评估中发现的高风险实施技术加管理的有效控制,将风险降低到可接受的程度,减小威胁发生的可能性和弥补技术管理漏洞。及时有效的测试和打补丁,员工入离职及转岗时,权限要及时调整到位等,做好所有的变更流程等,并且建议企业相关部门定期抽查;
- 规避风险——组织可以选择放弃某些可能引来风险的业务或资产。将重要的信息资料多重多地备份,比如产品研发、财务等重要资料可以备份到云端,可以使用企业网盘类产品实时对重要资料的备份,避免因为WannaCry勒索病毒而造成毁灭性损失;
- 转移风险——将风险全部或者部分转移到其他责任方,比如商业保险;
- 接受风险:所有预防措施都已经在可控范围之内,若发生安全事故,需要及时补救,将损失降到最低。
亿方云如何保障企业信息安全?
数据安全是企业选择云存储服务的首要前提,安全的文件管理和协作平台在保证用户对其数字资产绝对所有权的前提下,应当从数据存储与传输各环节的保密性、访问控制、数据备份、平台防护等不同角度,对企业用户存储在平台的数字资产实施全方位的安全保护。
企业用户在考察文件管理平台的安全性时,可以从数据隐私保护、数据存储方案、文件访问控制、平台运维能力、安全认证、延伸保障等6大维度进行比较。下文以亿方云例,详述各个维度应有的安全保障措施。
严密的数据隐私保护
- 传输存储全链路加密:文件上传下载使用HTTPS作为传输协议,传输过程中对文件本身进行了二次AES CTR 256算法流式分块加密,确保最终保存在亿方云平台的文件均为密文,且文件在传输以及存储过程中杜绝被窃取可能;
- “三权分立”的后台权限管控:文件加密的三个key分别由平台和用户进行三权分立的保管, 严防内部的数据泄露;
- 企业间数据隔离:亿方云对不同企业的数据进行独立的沙箱保护,确保企业间数据不可穿透;
- 灵活数据迁出通道:亿方云保障用户对数据的绝对所有权,提供网页下载、客户端同步等方式,让用户可以自由迁出数据。
防风险的数据存储方案
- 完整保留文件历史版本:亿方云将用户编辑修改的所有历史版本完整保存,当此次病毒爆发时,用户可以非常方便的将被感染加密的文件恢复到较早的历史版本;
- 多重备份:亿方云为用户数据做了多达四份加密保存,且数据分布在不同的存储平台,杜绝因平台原因造成的用户数据丢失;
- 容灾消灾:亿方云拥有强大的异地容灾备份功能,可在不同存储平台间快速完成数据切换而不影响用户的文件使用,紧急情况下迅速对用户数据进行容灾恢复。
全方位的文件访问控制
- 三种文件夹属性:个人/企业内协作/企业外协作文件夹,清晰区分不同内容的共享边界;
- 七级协作权限:细分至查看、预览、上传、下载、分享、删除、管理协作者等不同权限,灵活配置满足企业复杂的安全共享需求;
- 九大类操作日志:九大类超过60种日志,几乎覆盖用户在平台上的任何操作,便于企业管理员随时查询审计;
- 内容安全分享:支持加密/人员访问权限/访问期限等多重安全设置,确保对外分享内容在流转过程中的全程可控。
出色的平台运维能力
- 攻击防护:亿方云平台拥有抵抗各种网络攻击及入侵的能力,比如Ddos攻击、网络窃听等,并对异常访问流量有清洗过滤功能,同时配合阿里云云盾对平台底层进行安全加固;
- 完备的监控体系:从服务器负载、应用错误日志、后台服务运行情况、产品各个功能模块服务状况、数据变化趋势等多维度进行7*24小时实时监控预警,任何异常第一时间捕获并被处理,确保平台稳定;
- 高可用性:所有底层功能模块采用高可用负载均衡设计,各个模块均以120%的负压能力对外提供服务,任何集群模块中一台服务器发生故障会被自动剔除出集群,修复后会自动添加至集群,整个过程不影响平台可用性;
- 权威机构安全漏洞扫描:亿方云曾多次邀请Sobug资深众测平台对亿方云进行全方位安全体检,为企业数据安全再加一层保障。
国家标准的安全认证
- 公安部信息安全等级保护三级:该认证为公安部信息安全认证的最高等级;
- ISO20000& ISO27001双认证:亿方云通过ISO20000信息技术服务管理体系、ISO27001信息安全管理体系双认证;
- 可信云服务体系认证:亿方云是国内率先通过由数据中心联盟组织,中国信息通信研究院(工信部电信研究院)测试评估的可信云服务认证的企业文件云存储企业之一。
延伸的保障机制
- 企业数据安全保险:在为企业用户提供全方位的数据保障之外,亿方云还与国内最大的外资保险公司AIG旗下美亚保险合作,创新性地推出了企业云服务数据安全责任险。对于亿方云平台的企业用户来说,如因平台原因造成用户数据丢失或泄露,用户将获得最高100万美金赔付;
互联网是没有绝对安全的,数字时代,重视企业数据安全是一件永无止境的事情。对于企业来说,没有一个方案能够100%的保证企业文件的绝对安全,逐步建立对于企业信息完全防范的意识和预案至关重要,就现阶段而言,企业通过亿方云做好文件备份是关键。
 400-993-9050
400-993-9050 









 浙公网安备 33011002015048号
浙公网安备 33011002015048号