西北工业大学遭黑客攻击,高校及科研机构如何保障办公安全?
很多人可能都觉得,一所普通高校里的信息遭到了攻击,有这么严重吗?
但认真了解过这所学校,就知道这肯定不是小事了。

(西北工业大学,图片来源于西工大官网)
西北工业大学,被称为“国防七子”之一,是中国唯一一所以同时发展航空、航天、航海工程教育和科学研究为特色的全国重点大学。一直以来,该校作为隶属于工业和信息化部的知名高校,参与国家科技重大专项、武器装备型号项目研究,拥有8个国家级的重点实验室。
境外黑客向其发起攻击,很可能是试图刺探、窃取我国相关领域重要敏感数据和信息。

(西工大“飞天一号”发射成功,图片来源于西工大微信公众号)
可想而知,如果境外势力攻击成功、数据被窃取,将给学校乃至国家带来多大影响。幸运的是,西北工业大学通过较强的网络安全意识与技术防护措施,成功规避了重要数据的泄露,保障了师生信息安全。
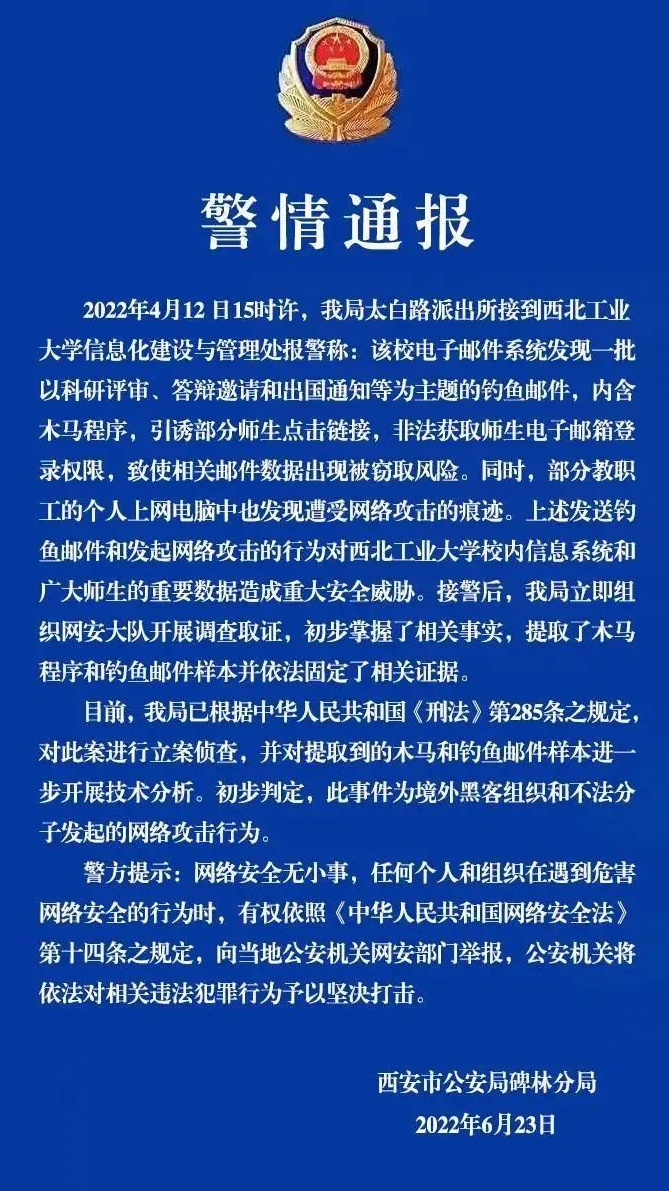
(西工大官方声明,图片来源于西工大微信公众号)
高校办公安全如何保障?
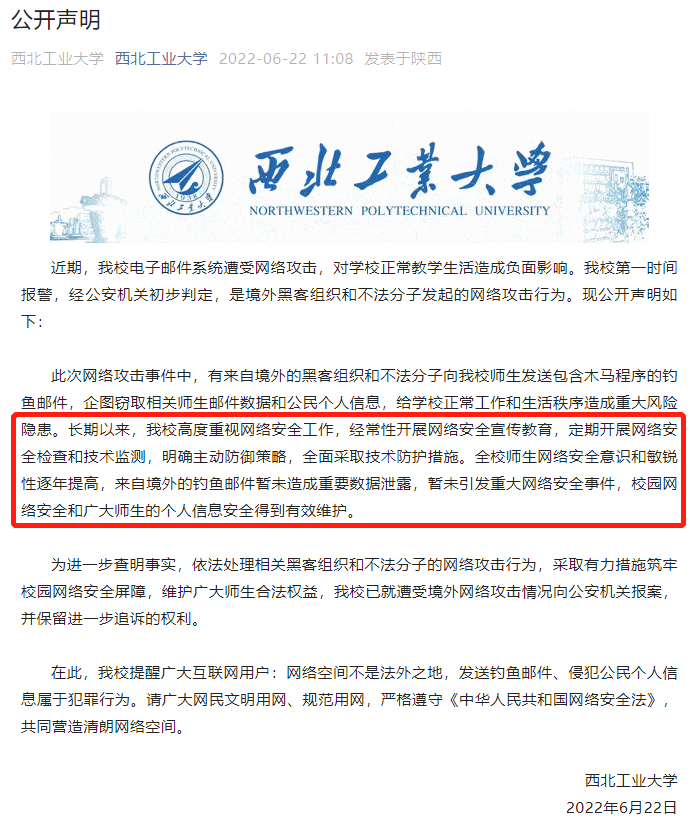
那么,360亿方云如何保障高校、科研机构、企事业单位遇到和西北工业大学一样的情况时,也能够成功粉碎网络攻击造成的数据泄露风险呢?
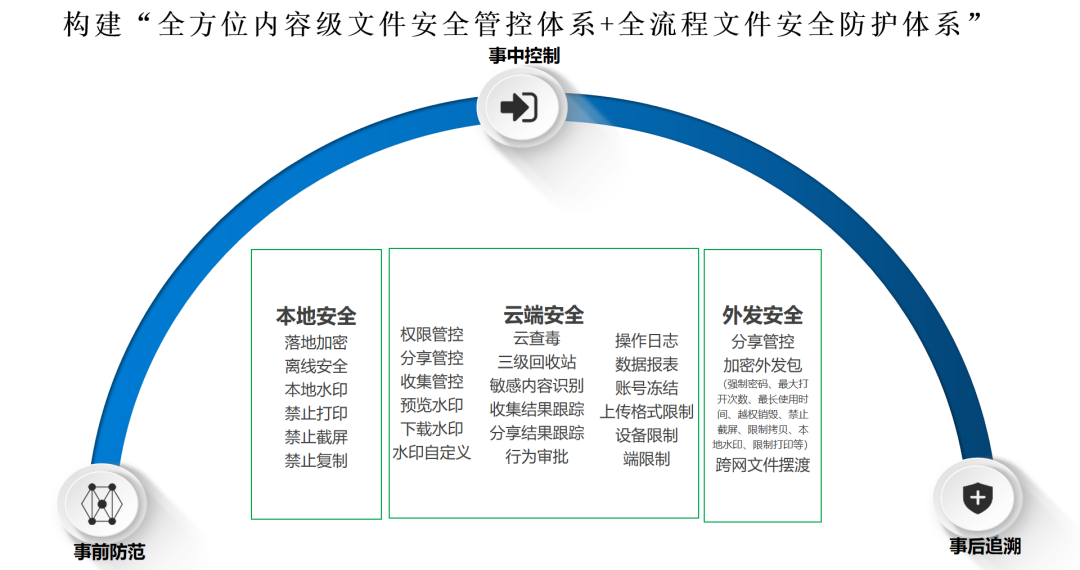
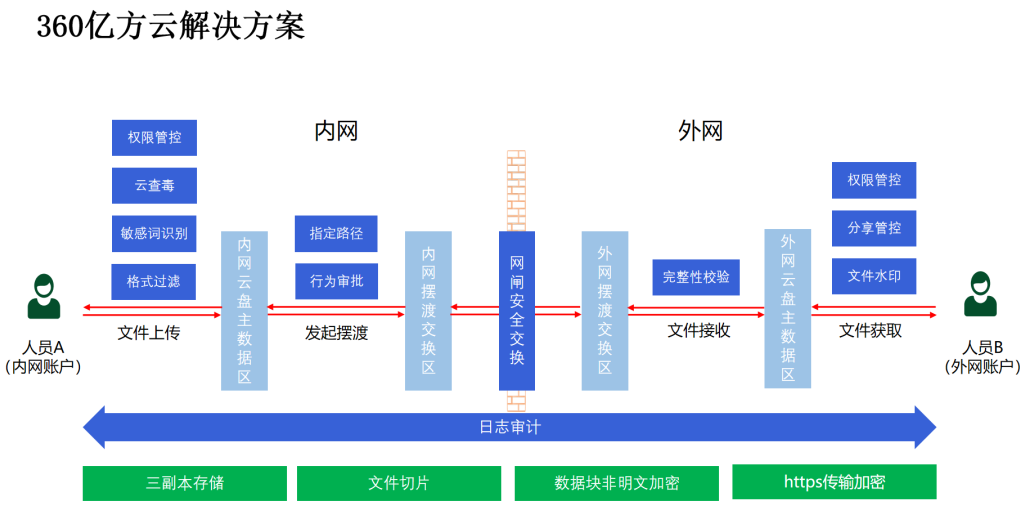
通过分布式存储架构、数据切片、数据加密存储、多副本分散存储、多种备份、异地容灾等多重机制,保障用户文件数据安全,规避黑客攻击后从服务器上获取未加密文件,从而导致数据泄露的情况发生。
亿方云在现有查毒引擎的基础上,新增了360云查毒引擎。
文件上传至亿方云平台时自动进行病毒查杀,解析到病毒文件后,系统会自动将病毒文件转移到隔离区,并提醒相关人员,从而避免感染了病毒的文件进入学校资料库,导致病毒文件扩散传播,殃及全部数据。

对登录的用户身份进行多重验证与审核,从源头处防范并杜绝安全风险。
限制成员只能在企业允许的区域登录亿方云。

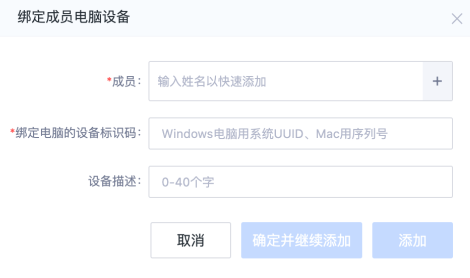
限定成员只能通过企业允许的操作设备登录亿方云。可以查看正在登录亿方云的设备,并删除不信任的设备,及时修改登录密码。
登录过程中对用户的账号进行二次验证,防止因账号密码失窃造成的数据泄露。
360亿方云文件跨网摆渡方案,可以在不打破网络隔离现状的情况下,实现多网之间数据的收发、摆渡、共享,建立可管控、可审计、安全合规、防止信息泄露的统一跨网文件交换通道。
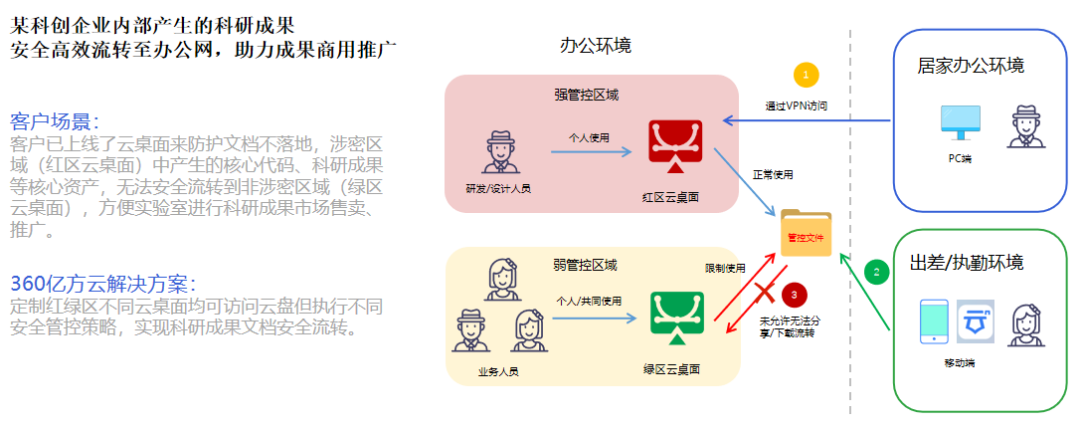
当文件需要从涉密区域流转到非涉密区域,进行商业化时,可以通过涉密区域云桌面上传至企业云盘,非涉密区域业务人员登录云盘,通过审批后即可下载相关文件,确保文件跨网流转安全、合规、便捷。
-
本文分类: 行业资讯
-
浏览次数: 6002 次浏览
-
发布日期: 2022-07-28 10:32:16
 400-993-9050
400-993-9050 









 浙公网安备 33011002015048号
浙公网安备 33011002015048号